Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.

Co-authored by Brennon Hampton
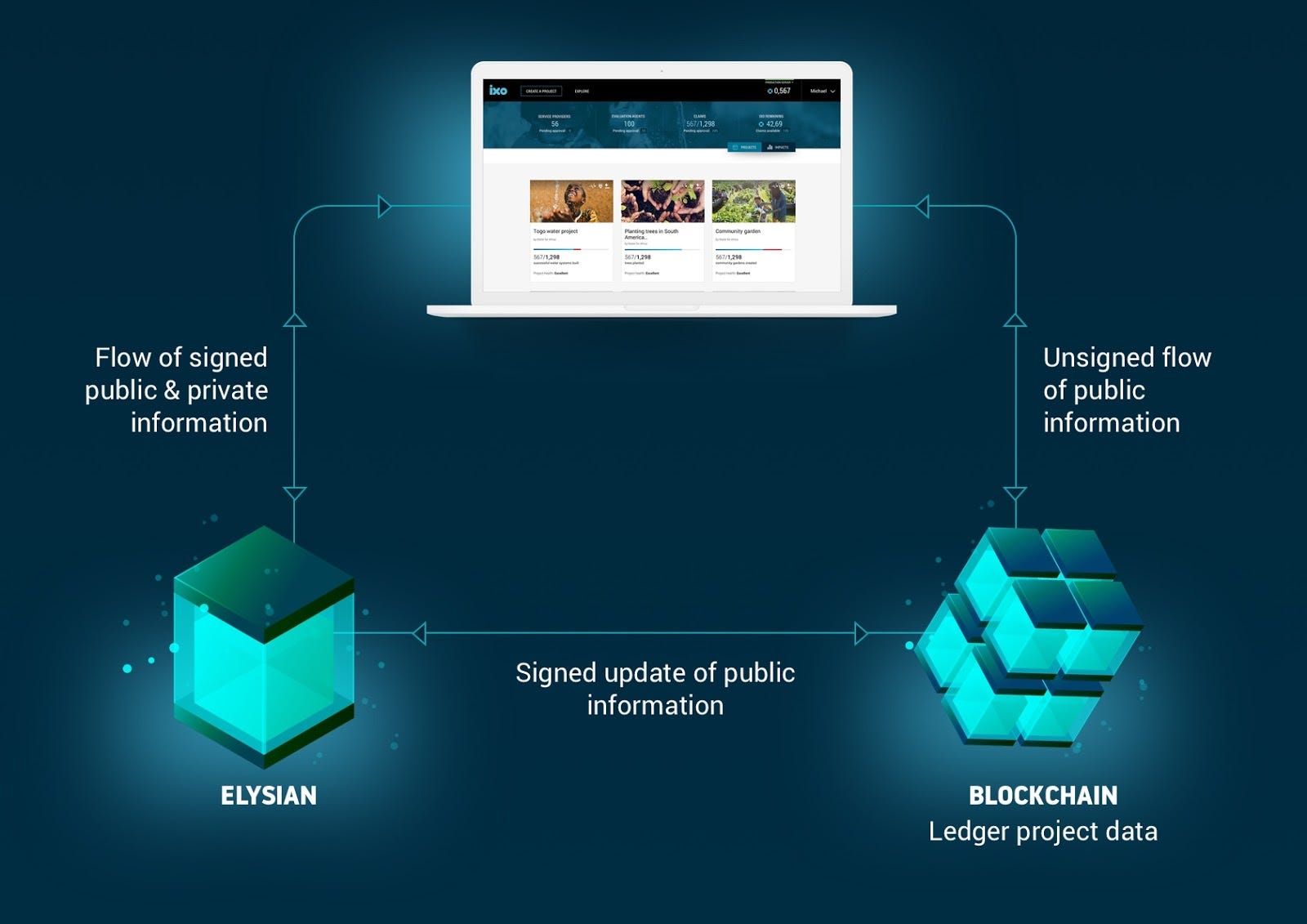
The ixo protocol defines how data packaged within cryptographically hashed and signed messages get processed and stored. In the context of ixo, these data resources are described as verifiable impact claims. It turns out that merkelized private data stores are a fundamental piece of the architecture for most web 3.0 applications that will have uses beyond the ixo protocol. We have ended up building a generic, highly configurable new database utility that implements core new Web 3.0 standards and uses hash-chains to ensure integrity.
Today we are excited to announce that we will make this available as an open-source release that we call Elysian.
The name Elysian derives from the Ancient Greek term for reserving admission in perpetuity to those chosen by the gods, the righteous, and the heroic.
The Elysian release of ixo data stores provides a powerful set of tools for controlling access to private data on a permissioned basis to those services that can prove their credentials and capabilities, using the W3C Decentralized Identifier (DID) specification. Only the chosen ones who have proven their credentials can access Elysian data stores, using the powerful capabilities of decentralized authentication and the magic of applied cryptography.
For ixo, impact data must be privately owned and access controlled by the creator of an impact project. The claims relating to a project will typically include sensitive information, such as personal identifiable data. The storage of this data must comply with jurisdictional, data protection and privacy regulations. We also want these stores to be censorship-resistant, with as little reliance as possible on central agencies to host project data. To be useful for the many applications of the ixo Protocol, these data stores need to be dynamically customisable, immutable, non-repudiable and only accept requests from verifiable digital identities, driven by their credentials and capabilities. The data stores must also be fast, cheap, secure and make it easy to perform queries on the stored data.
It turns out that these are core data storage requirements for many other Web 3.0 applications.
ixo
How these data stores are deployed in the ixo network, is that each project that is set up on the ixo network points to an independently hosted data store to which the project’s data will be directed. This data remains under the full private control and ownership of the project creator. What goes into the data store and who can write or read the data is set up dynamically and controlled at the level of the data store. This data storage is entirely ‘off-chain’ from the ixo network or any other public blockchain. However, the proofs of the data submissions are stored on the ixo public ledger, together with limited metadata that is extremely useful for tracking the performance of projects, indexing and locating the data. We call this the Global Impact Ledger.
As the signed messages containing project data (impact claims) are passed through the ixo blockchain for processing, these are validated by consensus and appended to the hash-chain record within the project’s data store. Effectively, each project has its own project hash-chain/s that have been validated. Refer to the ixo White Paper for more details about how the protocol then enables verification of these claims, tokenizes the proofs of impact and enables trading of these tokens and their underlying data.
Elysian data stores are highly customisable
On initialising an Elysian Data Store, a dynamically customisable list of identity credentials and capabilities is established to define what actions can be performed, by which of the identified agents that will interact with the data store. These permissions can be updated or revoked at any time.
Access control is fine-grained and complies with the consent requirements for data protection and privacy.
Data stored within an Elysian data store is immutable as this is an append-only data store (data cannot be deleted or updated).
All data operations are authenticated by confirming that the digital identifier relating to the service or agent that signed the incoming request has the capability to perform this action.
The data is all verifiable, as this conforms with the W3C standards for verifiable claims and credentials. Only message payloads that match the predefined JSON submission template set up for data store can be submitted. The associated credentials, such as cryptographic signatures, must also verify.
The public key associated with the digital identifier that signed the request is retrieved via the identifier blockchain record, from the identity credential provider and validated.
Once verified, we insert the record and log the transaction in a timestamped transaction log with a hash that includes the previous transactions hash.
To close the loop, for every verified message that passes into the Elysian data store, an event is triggered to the ixo blockchain.This ledgers the transaction and updates the publicly viewable project data.
A Web 3.0 data utility for all
With Elysian, we believe that we are providing a core building-block for many types of data-intensive Web 3.0 applications that will be fit for the purposes of decentralised architectures. We look forward to taking this into full production as a secure and highly useful piece of the data infrastructure for the ixo network. We encourage others to get involved in the project to help build out the exciting pipeline of features and uses of Elysian, as an open-source utility for all.
Learn more about ixo and how to get involved at ixo.foundation
- Follow ixo on Twitter
- Join the conversation on Telegram we’d love to answer your questions!
- Like ixo on Facebook
- See the code and contribute on Github
- We’re on Reddit too
- Subscribe to the ixo e-mail newsletter
- Email the team info@ixo.foundation
Elysian Release of the ixo Data Store was originally published in Hacker Noon on Medium, where people are continuing the conversation by highlighting and responding to this story.
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.