Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.
 Make a smart contract do things it didn’t want to…
Make a smart contract do things it didn’t want to…
This is a in-depth series around Zeppelin’s smart contract security puzzles. I’ll give you the direct resources and key concepts you’ll need to solve the puzzles 100% on your own.
Over the next weeks, we’ll reproduce how some serious hacks were induced, notably:
- $50M DAO hack: resulting from a re-entrancy problem
- $30M Parity hack: induced by a delegatecall() exploitation
Required: Basic knowledge of smart contract development
How Ethernaut works
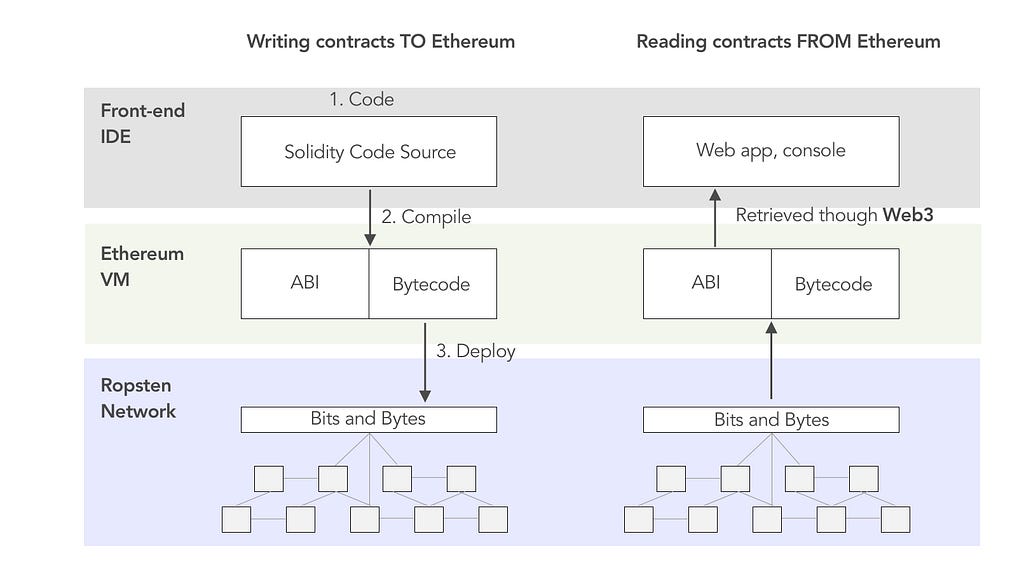
All smart contract source code are compiled into two formats, by the Ethereum Virtual Machine (EVM):
- Application Binary Interface (ABI): a communication layer between solidity and Javascript, in JSON format
- Bytecode: the low level machine language that gets executed by the the EVM
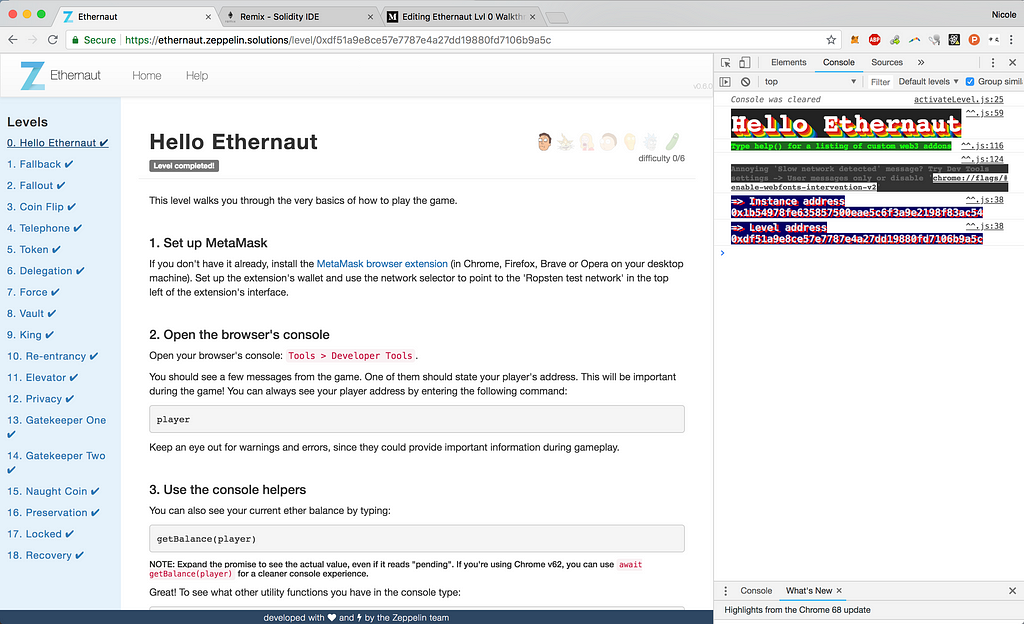
When you request get a new instance for each level, Ethernaut deploys the compiled bytecode to a new address on the Ropsten test network:
Once this new instance is created on the blockchain, its address is returned to your web client through an event, as seen in the game’s main contract, Ethernaut.sol:
Finally, Web3 wraps an ABI around this new contract instance, and allows you to interact with the contract through your web console.
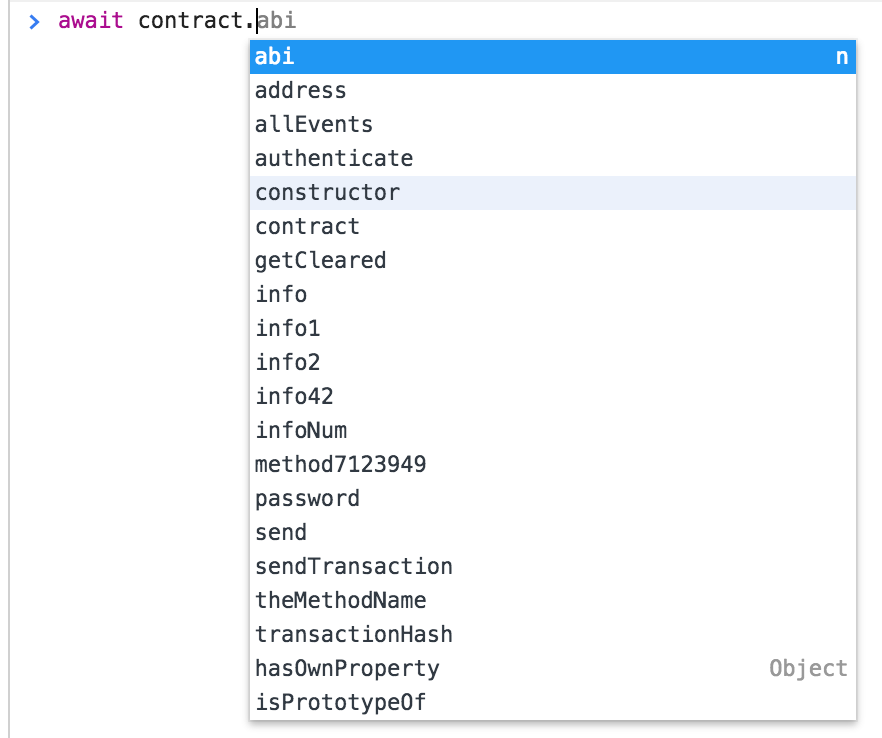 Notice that all `public` functions are available in the web client
Notice that all `public` functions are available in the web client
Detailed Walkthrough
This level requires you to guess a secret password in order to “get cleared” to move on.
- Notice that Ethernaut passed a secret _password into the constructor, when it created your contract instance:
function Instance(string _password) public { password = _password; }2. This password is stored as a public string variable
string public password;
3. All public, basic variable types in Solidity have an auto-generated getter function. This means you can directly read this not-so-secret password by typing into the console:
await contract.password()
You can use async/await to work with Web3 promises with more ease
4. To pass this level, simply call the final authenticate function and pass in the retrieved password, via the console:
await contract.authenticate("[password here]");You’ll be modifying storage in the authenticate function, so expect to pay some gas when calling this transaction.
5. Finally, you should be able to double check if you’ve passed this level:
await contract.getCleared();
Key Security Takeaways
- All functions and variables stored on the blockchain are viewable by the public
- Never store passwords directly inside a smart contract, (not even as private variables, as we’ll learn shortly)
More Levels
- Lvl 1 Fallback Walkthrough: How to abuse fallback functions
- Lvl 2 Fallout Walkthrough: How to abuse developer errors
- Lvl 3 Coin Flip Walkthrough: How to abuse pseudo randomness
Ethernaut Lvl 0 Walkthrough: ABIs, Web3, and how to abuse them was originally published in Hacker Noon on Medium, where people are continuing the conversation by highlighting and responding to this story.
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.