Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.
Crypto is Posing New Threats to Universities

Like it or not, universities are uniquely positioned to be susceptible to various kinds of exploitation and digital attacks as a result of the arrival of cryptocurrencies. The most challenging part is that these threats are difficult to identify until after the fact.
When you combine unfettered access to electricity, vast internal computer networks, large numbers of staff with administrative permissions and tech-savvy young adults, things are going to get interesting pretty quickly.
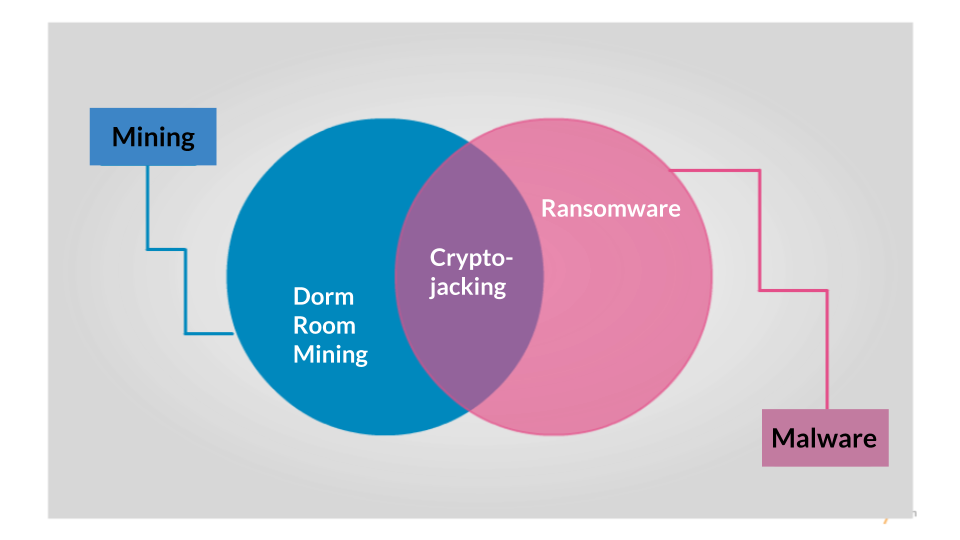
The threats come from two areas- malware and mining. We’ll get into the what, how and why later on. But first look at this venn diagram I spent seven minutes making.
Malware
If you’re new to Malware, let me explain how……ahh screw it. “Hey, Siri…”
So basically, malware is just shorthand for malicious software. It may infect a single host or an entire network by spreading through the digital plumbing. There are a number of types of malware out there; Adware, Spyware, Trojans. However, there’s one type that’s seeing explosive growth. Enter ransomware.
Ransomware
The most important technological shift to understand is that bitcoin brings, for the first time, a form of digitally-native value. The subsequent avalanche of other cryptocurrencies, some of which are anonymous, means that attackers have a convenient and hard to trace payment method with which to monetize security vulnerabilities.
“The problem that cybercriminals have always had, was how to turn data into currency. Now data is currency.”
-Oliver Rochford, Research Director at Tenable Network Security
Think of it this way- previously, if someone could hack into your email account they could read your emails or send spam from your address. Today, someone could compromise your email account and essentially hold it hostage, demanding that you pay them (in the form of a cryptocurrency) to regain access. Might not sound like a big deal, but if you apply the same method to say the reservations system of a major international airline. Shit. Gets. Real.
How does ransomware get into a system? Well, initially through a malicious link or attachment contained within a phishing email. Combine this with a networked computer running an outdated and exploitable operating system and you can potentially give up access to a lot of sensitive data. In targeted attacks, these can be very difficult to identify as shown by the example below (
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.