Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.
Security
Avoid the risk of supply chain attacks by buying from the official Trezor Shop or an authorized reseller.

Taking custody of your Bitcoin with a hardware wallet is the most effective thing you can do to improve security. As exchanges start revoking customers’ rights to their funds, it’s high time to take control of your keys.
If you’re looking to buy a hardware wallet, make sure you buy it directly from the Trezor Shop.You can also check our list of official resellers for authorized alternatives. Never buy a Trezor from an unauthorized third party, as you can never tell who may have had access to it before you.
Read on to learn what to look out for when making a purchase, what to check when your wallet arrives, and how we are continuing to improve security for customers.
What to look out for and how to detect tampering
To keep your Bitcoin safe you need to know where it came from, so that you can be sure you’re the only person in possession of your private key. That’s why hardware wallets must always be bought from an authorized seller.
There are ways to tell if a device has been tampered with, but it is better to avoid the uncertainty when it comes to protecting your Bitcoin. Beware of illegitimate vendors and phishing sites imitating official channels.
We recently discovered a small batch of counterfeit devices being sold on a popular Russian marketplace, despite the site not being an authorized reseller and therefore not stocked by us. Since we are not currently able to deliver to Russia due to the war, this incident appears to take advantage of the demand for hardware wallets and is using unofficial channels to sell devices which have had components replaced in order to trick buyers into storing their funds where they can be stolen.
On investigating some of the devices we found that they do not function as intended, and that the casing had been opened to access the internal components, leaving faint signs of tampering. While no such incidents have been reported outside of Russia, similar schemes targeting Bitcoin users in the past have been seen.
Never purchase hardware wallets from unverified sources, it’s not worth the risk. The official Trezor Shop is the safest way to buy a Trezor and we deliver worldwide. We also have an Amazon store, or you can use an authorized Trezor reseller listed on our website.
If you’re ever in doubt, verify the authenticity of your device using the methods described below.
Firmware checks
There are several layers of security in place to prevent supply chain attacks. A legitimate device will always arrive without firmware installed. Firmware is what makes the device function and is installed by the user when first setting up their Trezor.
The bootloader, which controls the hardware, is installed at the factory and verifies the firmware you install, to make sure it has been signed by SatoshiLabs and not someone else.
Using Trezor Suite, you can check which firmware version is running on your device by going to Device Settings and scrolling to the header Firmware version. Alternatively, switch your device to Bootloader mode to see both the firmware and bootloader version on your Trezor screen.
The bootloader can confirm the firmware is correctly signed, which is a good sign it is safe to safe to use your device to generate keys. In the case study below, however, internal components were substituted making this redundant, but there were other tell-tale signs of compromise.
Tamper-evident seals
Both models of Trezor use holographic stickers to show authenticity, and the box of the Model One is glued shut meaning it must be broken to access the device. These measures can reveal if the package or device has been used since leaving the factory.
While packaging can be damaged in transit without meaning the device has been compromised, it offers a quick and easy warning to pay extra attention to other security features such as the firmware signature or any irregularities to the device’s plastic casing, which could indicate an attack.
Device casing
The photos below show a side-by-side comparison of the casings of a genuine device bought from an official seller and a compromised device. The Trezor on the top is genuine, while the one on the bottom has been broken apart and modified.
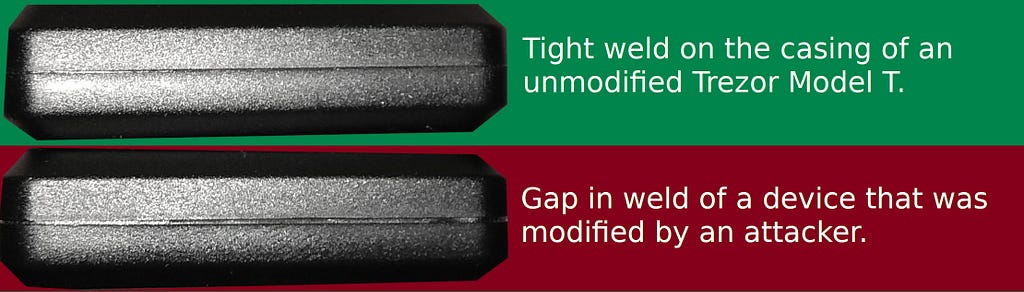
View of the top seams of a genuine (green) and compromised (red) Trezor device.
If you look closely you will notice a difference in the welding: the genuine device shows a smooth seam, while the seam on the fake device shows signs of being opened and resealed. Notice the wider gap in the welding on the counterfeit device, as it does not fit together properly anymore.
A simple test to check if a device has been opened is to give it a gentle squeeze. The seams of devices in this compromised batch will visibly close over, while a factory-condition Trezor should not move.
Security improvements to prevent tampering
We want our customers to feel absolutely confident in the authenticity of their devices when unpacking them, so we are introducing new security measures which should further diminish the chances of tampering. These are also designed to clearly warn users of any tampering that could have taken place since leaving our production line.
Improvement of packaging
We are researching new innovative ways to secure our devices and their packaging to provide an even higher level of assurance to customers. We currently use holographic seals to cover the USB port of the device on the Model T but this does not protect against the case being forced open, so we have begun working on a new type of packaging that will allow you to more easily notice whether the device was tampered with on its journey to you.
Software improvements
We are implementing a solution which will enable us to verify what kind of firmware is installed on the device. Both Trezor firmware and Trezor Suite will receive an update which will allow them to automatically compute hashes of the firmware installed on connected devices. Such hashes will then be compared with genuine firmware versions available from Trezor. This will be an additional check on top of the bootloader process which checks the firmware is correctly signed.
Hardware component bonding
To make it even harder for malicious actors to exchange internal components, we will implement even tighter bonding between affected components and the board. During production, individual chips will now be glued onto the board, meaning an attacker would have a higher chance of damaging the device should they try to tamper with it. Although it can not completely prevent attackers from tampering with the device, it will make it more difficult and costly, increasing their chances of failure.
Should you be worried about fake devices?
If you bought a device from an official source it is highly unlikely that there is anything wrong with your device. If there are signs of tampering when your order arrives, or you bought it from an unauthorized reseller in Russia, just reach out to Trezor Support or start a discussion on Trezor Forum and we’ll walk you through how to check for compromise.
Case study: fake Trezors sold in Russia
In the past month we learned about several incidents where modified Trezor devices were being sold on Russian marketplaces. Devices were running a version of a bootloader which had not been released.
To check a device bought from an unofficial vendor, the firmware and bootloader versions can be compared to official versions on GitHub:
- Model T: firmware, bootloader.
- Model One: firmware, bootloader.
On investigation we discovered other signs in common:
- Many of fakes sold on Russian marketplaces displayed a message when trying to sign a transaction: -26: non-mandatory-script-verify-flag (Signature must be zero for failed CHECK(MULTI)SIG operation)
To save any funds sent to a malicious wallet displaying this message, the seed should be imported into a genuine Trezor or another wallet. It should then be possible to sign the transaction and send the funds to a secure address.
- Trying to update firmware shows as a success but the malicious firmware remains.
- Some functions such as Shamir backup were not functioning on devices we investigated.
- Seeds generated by the counterfeit devices were predictable or, in some cases, predefined and did not change when the device was set up again. The passphrase function was also modified.
- All devices were obtained from vendors on the Russian market.
- The issue was mostly present on Trezor Model T devices.
- Some internal components had been replaced, allowing the malicious actors to spoof the device’s behavior and make its security features redundant.
Users with compromised devices suffered similar problems using various cryptocurrencies, including but not limited to Bitcoin, Dogecoin and Ripple. Some of the problems faced, especially not being able to access passphrase-protected wallets, were also experienced when using third party wallets and importing the seed.
This was a rare and quite sophisticated case, showing that the attackers would have practiced on many devices before creating the ones sent to victims. Unfortunately they were able to sell some of their fake devices due to the lack of alternatives on the market in Russia at the moment. There is potential for this to happen in other countries, though we have not heard of any cases reported, so it is best to watch out for red flags such as places selling wallets when none are available from official vendors, wallets for suspiciously low prices, or from unknown sources.
Stay safe shopping for hardware wallets was originally published in Trezor Blog on Medium, where people are continuing the conversation by highlighting and responding to this story.
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.