Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.
Authored by Huobi Research Institute researchers Yeyan Wei
Abstract
Looking back at the development of blockchains in recent years, new chains featuring high performance, PoS consensus, and smart contracts dominated the main market in 2021. In the entire blockchain track, Ethereum’s high gas fee and network congestion have led to more users choosing fast, low-cost, and dynamic new chains. The influence of Ethereum was gradually eroded, and the proportion of TVL fell below 60% at one point. However, with the onset of the bear market, these new chains have been hit hard, and many problems became more prominent, such as the collapse of Terra. Nonetheless, the narrative of the blockchains will continue in the next cycle, and the multiple chains will coexist for a long time. The fundamental reason is that no single chain can meet all needs. Moreover, upper-layer applications based on the blockchain infrastructure will also proliferate. How to achieve the interoperability of these applications and the smooth flow of asset information between different ecosystems are the challenges the cross-chain infrastructure needs to solve.
Generally, there are two ways to make asset cross chains: 1. Centralized exchanges; 2. Cross-chain bridge technology. This report mainly discusses the existing cross-chain bridge technology, and disassembles the mechanisms according to the three processes that cross-chain information needs to go through, including information transmission, verification and asset transfer modes. In this report, the implementation process, advantages and disadvantages of various mechanisms are explained using specific cross-chain bridge projects. Based on the performance of the cross-chain bridge, we analyze the cross-chain time, cost, and security, and users can choose the appropriate cross-chain bridge according to their needs. At present, there are indeed many challenges in the cross-chain bridge that need to be solved and upgraded urgently, especially in terms of interoperability. And there is greater expectation that the emergence of cross-chain smart contracts can pave the way to the interconnection of thousands of chains in future.
1. The Basic Concept and Value of Cross-chain
There are assets in the form of tokens on each blockchain, some of which are native assets of the blockchain, and other assets defined by smart contracts. These assets reflect the value and demands of the blockchain. Since blockchains come with various attributes, such as high-performance or privacy chains, and these chains provide a variety of applications and different revenue products, users can choose different blockchains and on-chain applications. This also gives rise to the need for asset cross-chain transfers. Actually, assets of different blockchains cannot be transferred directly at the physical level, and native assets can only exist on the original chain (with the exception of multi-chain networks). Therefore, the transfer of most assets is not native, but a kind of “pegged” asset corresponding to the transferred asset. Due to the diversity of cross-chain projects, it is difficult to count the total number of cross-chain assets. But we can acknowledge the growth of cross-chain demand from the BTC cross-chain assets.
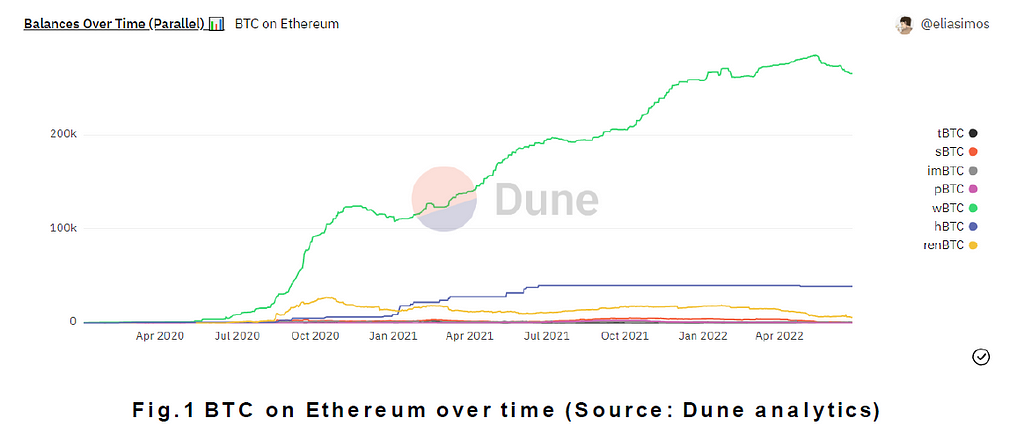
The cross-chain asset with the largest growth in Fig.1 is wBTC, whose full name is Wrapped BTC. An ERC-20 token pegged to BTC issued on Ethereum, it was jointly launched by blockchain projects such as BitGo, KyberNetwork and Ren in January 2019. The current total market capitalization has exceeded $5 billion. It is precisely because of the existence of this wrapped token that long-term idle Bitcoins can generate huge returns and improve the efficiency of capital flow between blockchains.
The cross-chain of assets is just part of the information transfer, with the other part to achieve interoperability. The latter refers to the ability to access and check information among blockchains, including calling each other’s functions and applications. Simply put, interoperability allows users to seamlessly participate in on-chain interactions across multiple blockchains. Cross-chain technology has formed different solutions and each has its own characteristics.
1.1 Cross-chain solutions
There are currently two cross-chain solutions in general, on-chain and off-chain. The off-chain approach is done through a centralized exchange. Some capable centralized exchanges have assets on a variety of chains. For example, Alice wants to transfer USDC on Ethereum to Avalanche. From Alice’s point of view, she needs to send USDC to the Ethereum address of the exchange. Then, she could see the recharged USDC in the account, and withdraw it to the Avalanche network. From an exchange perspective, it needs to have accounts on both Ethereum and Avalanche, and have USDC assets issued on Avalanche. When the exchange confirms the user’s withdrawal, it can directly send USDC to the user’s Avalanche address. Cross-chain through centralized exchanges is based on the premise that users trust the exchange and the Web2 network. In terms of user experience, this is faster and cheaper (taking less than 5 minutes, and the transaction fee mainly depends on the gas fee on-chain).
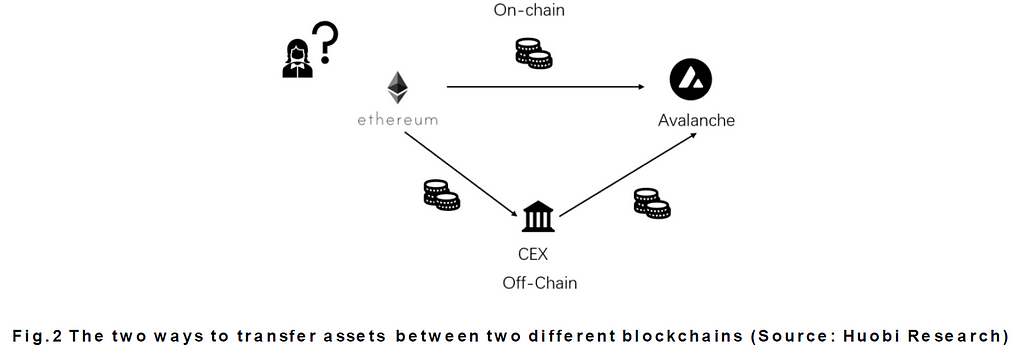
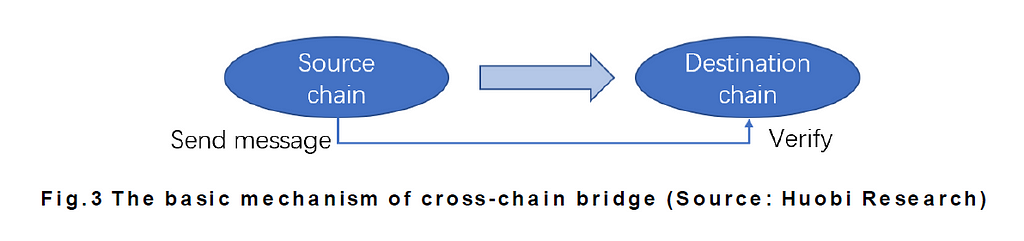
The on-chain cross-chain approach is through the cross-chain bridge. Cross-chain bridges exist mainly because people are not satisfied with the off-chain method, and hope to realize the true vision of “Internet of blockchains” through the direct decentralized exchange of assetson-chain. A cross-chain bridge is a tool that connects two blockchains for assets and data to interact. The essence of this interaction is the process of the source chain sending information and the destination chain receiving and verifying the information. Currently, more than 100 cross-chain bridge projects have been used to realize cross-chain between different Layer 1 and between Layer 1 and Layer 2. The cross-chain bridge is the infrastructure in Web3, so this report mainly analyzes the mainstream cross-chain projects from the perspectives of technology and security.
1.2The development of cross-chain technology
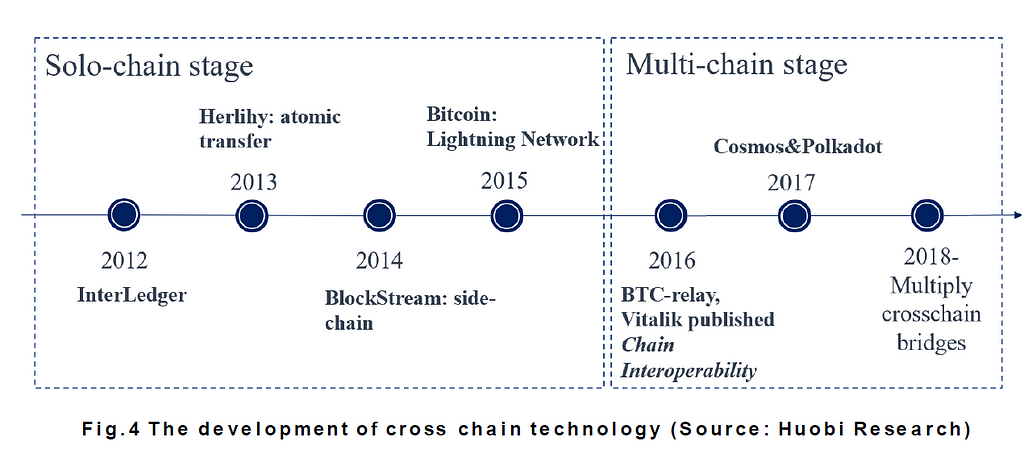
Cross-chain technology has been studied since the birth of Bitcoin. We can simply divide the development of cross-chain technology into two stages, namely the single blockchain stage and the multi-chain network stage.
Single blockchain development period (2012–2015): As early as 2012, Ripple Labs proposed the InterLedger protocol, which was officially applied in the Ripple blockchain until 2015. The protocol uses a third-party named Connector to create fund custody and transaction verification for both parties across the chain. In 2013, Herlihy proposed the concept of atomic transfer, which means that the sub-transactions that constitute a complete cross-chain transaction occur at the same time or do not occur, with no third intermediate state. This solution was upgraded to a major cross-chain mode, the hash lock mode. In October 2014, BlockStream proposed the concept of side chain for the first time, which uses a two-way peg mechanism to transfer encrypted assets between the side chain and the main chain. In 2016, BlockStream further proposed a sidechain with strong federation, which effectively reduced the delay between the side chain and the main chain and improved interoperability by introducing multi-signature technology. In 2015, Lightning Network proposed the application of the Hashed timelock mechanism to open a fast transaction channel off-chain, which improved the transaction efficiency of the Bitcoin system.
Multi-chain network period (2016-present): In 2016, BTC-Relay proposed a relayer mechanism to realize one-way cross-chain communication from Bitcoin to Ethereum. In the same year, Vitalik conducted a detailed and in-depth analysis of blockchain interoperability issues. In 2017, the multi-chain network Polkadot and Cosmos formed the blockchain platform conception, which can realize cross-chain native assets of homogeneous chains. Meanwhile, the demand for various single chains continues to grow, as do the cross-chain projects.
2. Interpretation of Mainstream Cross-chain Technology
The basic principle of the cross-chain bridge is to provide a communication channel between two blockchains, and its implementation mechanism for asset transfer can be divided into three processes: 1. Information transmission; 2. Information verification; 3. Assets transformation. Cross-chain bridge technologies adopt different solutions according to the deployment cost and technical difficulty. We interpret the technologies currently used by mainstream cross-chain projects based on these three processes.
2.1 Transformation of cross-chain information
The destination chain needs to receive cross-chain requests from users of the source chain, but without special tools it is impossible to transfer information between different blockchains. The basic condition for cross-chain information transmission is that a cross-chain bridge needs to deploy smart contracts on-chain. The purpose of the contract is two-fold: 1. To monitor the transaction information related to cross-chain; 2. To establish capital pools. The on-chain dynamics of contracts require some off-chain roles to monitor and pass these cross-chain messages from one chain to another. And these off-chain roles have differences in terms of being centralized or decentralized. Centralized roles include market maker teams and validators of some capital pools, and more decentralized roles include Chainlink oracles and relayers or relay chains. Communication would not be possible without the participation of these off-chain roles.
The cross-chain information received by the off-chain roles generally includes: the number and type of cross-chain assets, the address information of the destination chain, and other transaction-related information. This information is transmitted in a compressed format, and some may only contain Merkel proofs of the block header.
2.2 Cross-chain information verification mechanism
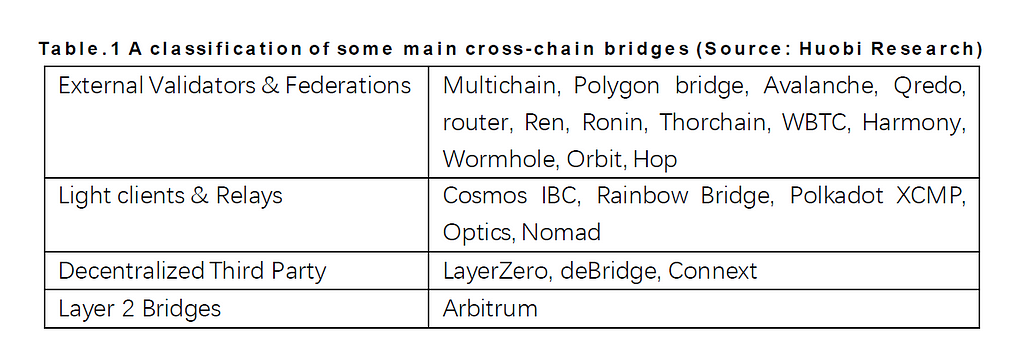
Before the cross-chain information is transmitted, it needs to be verified. The object of verification is the transaction information on the source chain, which requires the block header on the source chain. At present, there are four mechanisms for the cross-chain information verification: 1. Multi-party external validators; 2. Light client/smart contract; 3. Decentralized third-party validators; 4. Layer 2 bridges. The following table classifies some popular cross-chain solutions.
(1) External Validators & Federations
The most widely used verification method for the cross-chain bridges is multi-party external validators. Under this mechanism, there are one or more validators or federations to monitor the cross-chain contract address on the source chain. After the address receives the cross-chain asset, the validators sign the transaction, then the destination chain can take action. This mechanism is characterized by high speed and multi-point validators. There are two methods for technical implementation: multi-party calculation (MPC) operating threshold signature, or multi-sig. These two differ in the way that validators own the private key. The validators under MPC mechanism each own a part of the private key, and they need to jointly form a private key to complete transaction verification. Under the multi-sig mechanism, multiple validators have complete private keys, but the verification of the transaction requires the majority of these validators to sign it.
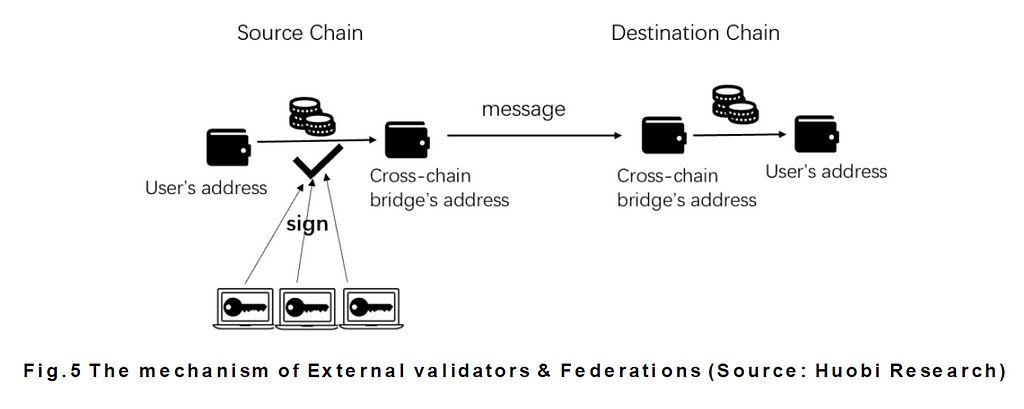
The cross-chain interaction between EVM compatible chains is simpler. Regardless of the decoding of the block header or cross-chain information, the validators do not need to do much technical processing work. But the cross-chain technology between EVM-compatible chains and non-EVM chains is more complicated. In the Wormhole cross-chain bridge, the 19 guardian node validators need to run complete nodes for each connected chain and use multi-sig for consensus. Wormhole is easier in technology, but the deployment cost is high, and it is currently one of the few cross-chain bridges in Solana.
(2) Light clients & relays
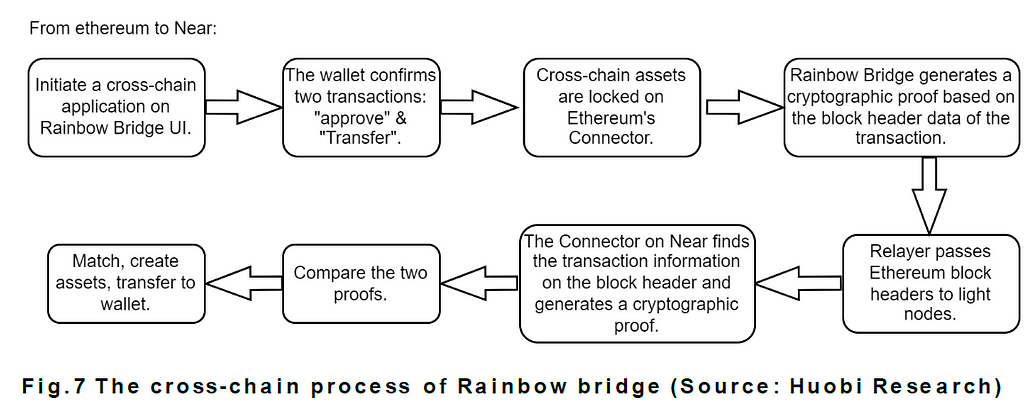
The first mechanism above seems a little bit centralized, and some cross-chain bridges have a very small number of validators, resulting in serious attacks. The rainbow bridge of Near uses a decentralized verification method to interact with Ethereum. This mechanism is extremely expensive to implement. Rainbow bridge requires three roles to operate together: light clients, relays, and connectors.
Light clients: Rainbow bridge has established a light client on Near and Ethereum respectively, which only stores block header information. The light client on Ethereum stores Near block headers, while the light client on Near stores block headers on Ethereum.
Relays: These are scripts that run off-chain on servers. Relays periodically read blocks from one blockchain and pass them on to light clients running on another chain. That is, the relay keeps the data of the light nodes up to date.
Connectors: These are smart contracts deployed on Ethereum and Near, responsible for cross-chain management of specific asset types. Similar to light clients, they come in pairs.
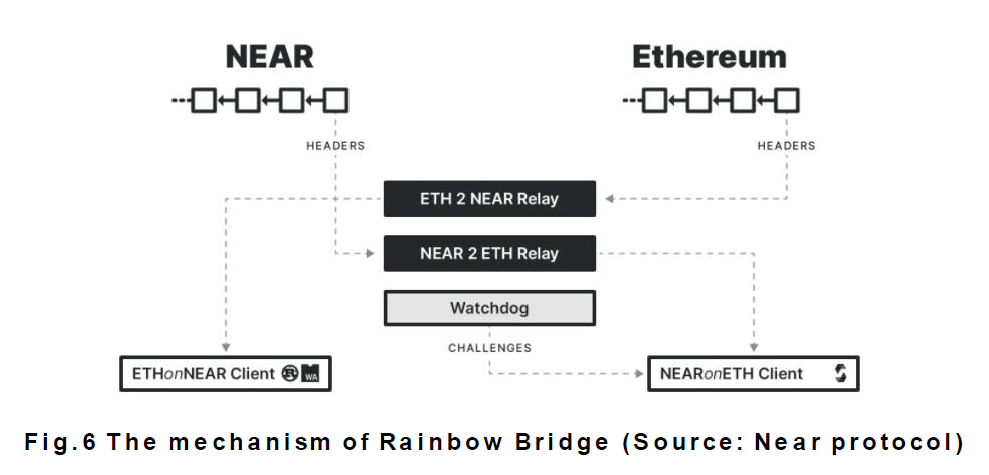
The following figure shows the cross-chain process from Ethereum to Near, and describes the operation mechanism of Rainbow bridge and the coordination of the three roles.
In addition to Rainbow bridge, the cross-chain protocols of Cosmos and Polkadot belong to relay verification. Light clients and relays are grouped together because they complete the verification process natively within the blockchain system. In Cosmos or Polkadot ecosystem, the validators of the hub or relay chain finish the cross-chain information verification. Because of the unity of the bottom layers, the cross-chain protocol in multi-network system can realize the cross-chain interaction of native assets and other information transmission through the direct compilation of block information.
(3) Decentralized Third Party
The concept of decentralized third-party verification is not particularly clear, but it serves to distinguish it from external validators and federations. This mechanism will introduce a decentralized third party as relays or validators. This third party can comprise sufficient decentralized nodes or other decentralized infrastructure.
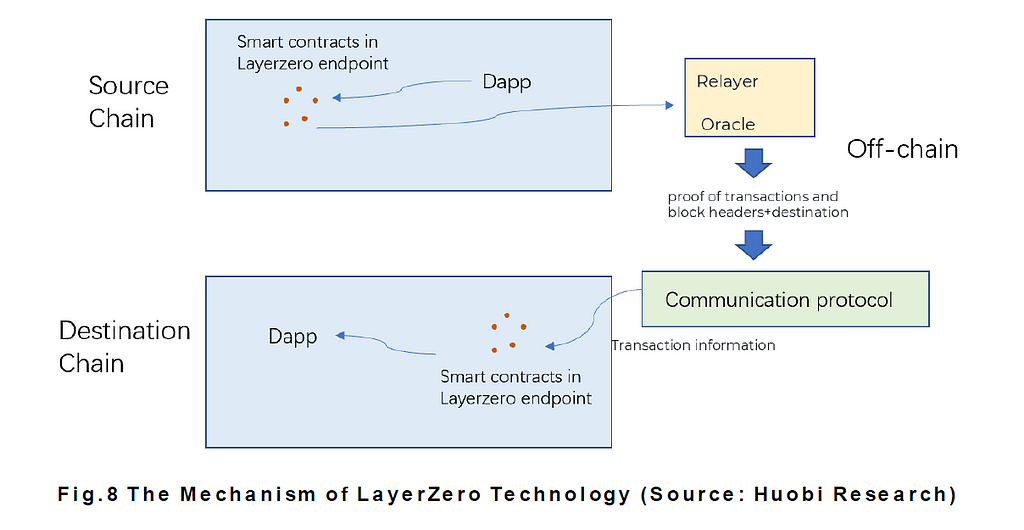
LayerZero is a representative project. It is not a cross-chain bridge, but builds the bottom layer of interoperability, enabling Dapps on different blockchains to pass messages. LayerZero is similar to Rainbow bridge, which deploys smart contracts on-chain. The difference is that two off-chain roles, oracle and relayer, are introduced to do the validator thing, and the two roles are independent of each other. Oracle chooses Chainlink, and there is no limit to the number of relayers, which ensures sufficient decentralization. When the transaction proof submitted by the two roles is consistent, the smart contract of the destination chain will execute the cross-chain transaction.
(4) Layer 2 bridges
Layer 2 technology has evolved over several generations, including sidechains (2014), Lightning Network (2015), Plasma (2017), and Rollup (2018). Different scaling technologies adopt different cross-Ethereum solutions. The cross-chain of sidechain technology requires a set of strongly trusted validators, and the sidechain does not keep pace with the state of Ethereum. Lightning Network uses RSMC and HTLC technology to complete asset transactions. In Plasma, operators are responsible for receiving transactions and data storage, and users need to submit transaction information and state update to Ethereum by themselves.
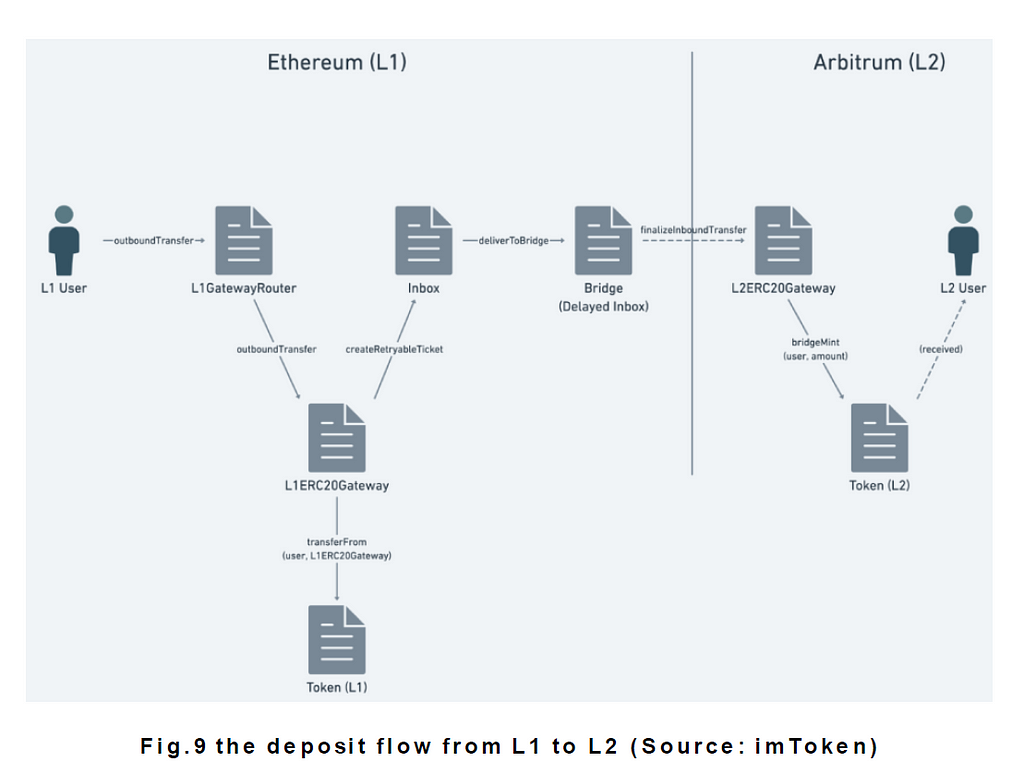
At present, Rollup is most likely to achieve the best performance in Layer 2 solutions. And there are Optimistic Rollup and Zk Rollup. Layer 2 inherits the security of Ethereum, so its cross-chain mechanism can be more centralized. Arbitrum has the largest number of users and TVLs of the Layer 2 solution. It is a type of Optimistic Rollup. Here we take Arbitrum’s native cross-chain bridge as an example to explain how it interacts with Ethereum.
Layer1—Layer2
When user Alice wants to transfer assets from Ethereum to Arbitrum, the cross-chain information is sent by the Inbox contract. After receiving the user’s message, Inbox will package the data in a basic format. The packaged message will then be forwarded to the Bridge contract for storage, and wait for Sequencer to periodically synchronize unprocessed messages to Sequencer Inbox. Bridge also sends the cross-chain information to the L2 Token Gateway contract on Layer2 to complete the cross-chain operations from L1 to L2.
Layer2—Layer1
In Arbitrum, Layer 2 transactions are sent to the Layer 2 sequencer, which merges, compresses, and sorts the transactions. The operator submits the compressed transaction data and the off-chain state transition proof to the Ethereum mainnet, which is written to the Sequencer Inbox contract on L1. The cross-chain information needs to wait for a challenge period (7 days), after which it will be written into the Outbox contract of L1 if there is no objection. The user needs to actively request the Outbox contract to execute the transaction.
From above, we can see that Layer 2’s cross-chain transactions are executed based on smart contracts, and the only centralized role is Sequencer, which only processes transactions and does not verify the accuracy of cross-chain information. The cross-chain from L1 to L2 is a decentralized trustless mechanism based on the security of Ethereum, while from L2 to L1 is based on proof and challenge periods. The verification process is entirely left to the cross-chain bridge itself.
2.3 Cross-chain asset transformation mode
There are two ways to deal with cross-chain assets: custodial and non-custodial. xDAI and wBTC are managed by a centralized institution for cross-chain assets custody, that is, the assets deposited by the user in the original chain are hosted at the address supervised by the cross-chain bridge. There is also a non-custodial type, where the asset is deposited in smart contracts or liquidity pools. This just illustrates how the custody of assets is handled on the source chain, but what is the actual process of cross-chain asset transfers? There are three ways here: 1. Liquidity pool mode; 2. Lock-minting/redemption-burn mode; 3. Atomic transfer.
(1) Liquidity pool mode
The liquidity pool mode in cross-chain ensures there are enough assets in the pools. This liquidity pool is characterized by unilateral flow. If there is insufficient liquidity in one pool, the cross-chain transactions may not be succussed. This type of cross-chain bridge generally supports limited assets, usually BTC, ETH, and some stablecoins.
The specific process is that there is a unilateral liquidity pool in source chain A. User Alice puts USDT into the pool. After chain A confirms the reception of the transaction, it will transmit the information to target chain B. The liquidity pool releases the corresponding amount of USDT (deducting the service fee and gas fee) to user Alice’s address on chain B, and user Alice receives the native assets on the chain B, not the wrapped assets.
The liquidity pool mode is the most frequently used, and sometimes requires an intermediate asset, such as RUNE in ThorChain, and “AnyToken” in Multichain. Taking Multichain as an example, “AnyToken” is a replacement token minted by the destination chain when the cross-chain liquidity is insufficient. Once the assets of the destination chain reach a sufficient level, “AnyToken” can be directly exchanged for the corresponding token.
(2) Lock-mint/burn-release
Another common cross-chain bridge applies the “lock-mint” and “burn-release” mechanism. For example, user Alice sends the cross-chain assets to the address of cross-chain bridges in source chain A, and specifies the address of target chain B. Off-chain roles may “send” this necessary information to chain B, and the cross-chain contract on chain B “mints” the corresponding tokens and sends them to Alice’s address in chain B. Such minted tokens are called “wrapped” tokens, such as wBTC and wETH. When users want to transfer assets from chain B to chain A, the assets of chain B will be burn, and the assets locked in chain A will be released.
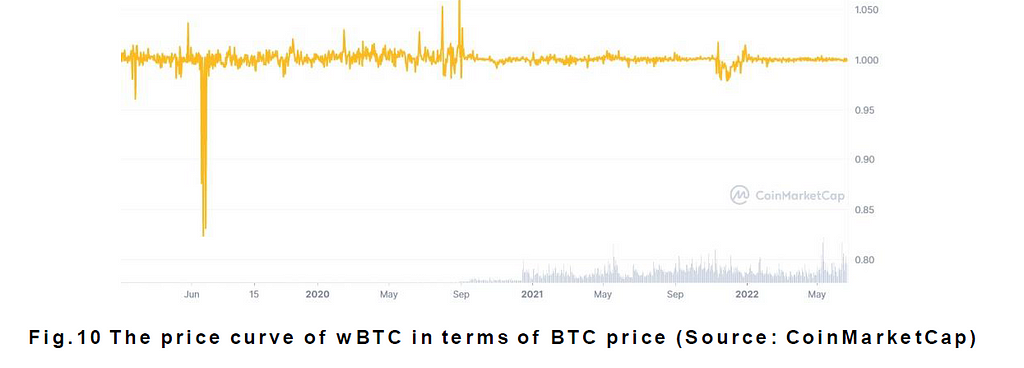
The value of wBTC and wETH depends on the BTC or ETH locked in source chain A. Normally, WBTC is at parity with BTC, but de-pegging can also occur in extreme situations depending on the market demand for WBTC. WBTC does not belong to the stablecoin of BTC, so there is no such thing as pegging to the price of BTC. WBTC is more similar to the conversion right of BTC. However, once the locked assets of source chain A are stolen, the smart contract cannot exchange the “wrapped” tokens, and they will be worthless. The advantage of this mechanism for cross-chain projects is that there is no liquidity problem, and assets can be transferred at any time. The asset transfer of Layer 2 also takes place through such a mechanism.
(3) Atomic transfer
Atomic transfer is a solution that can directly exchange assets on the source chain for assets on the target chain. Atomic transfer is the least trusted method among the ones available. Cross-chain bridges that use this method include cBridge and Connext. Atomic transfer is based on the hash time-locking mechanism, which is more like a peer-to-peer model. This is a cryptography approach without validators. The following is an example of the exchange of 1 BTC of user A in chain A with 10 ETH of user B in chain B, to illustrate the principle and implementation process of atomic transfer:
User A generates a random password, calculates the hash value m=hash(s), and sends m to user B;
User A uses m and a time t1 to generate a contract transaction on chain A, which locks the token 1BTC that user A needs to trade, and the lock time is t1.
User A sends m to User B, and sends the transaction to Chain A, proving that 1BTC has been locked on-chain;
User B uses m and time t2 to generate another contract transaction, locks 10 ETH and trades on-chain, and the lock time is t2<t1;
User A shows the password s to complete the transaction established by user B. Here, user A has disclosed his password r, so after user A obtain 10ETH from user B, user B can obtain 1 BTC through password s.
Atomic transfer has limitations. First, the transaction may fail due to one trader changing his mind. Second, both traders must be online at the same time. Third, one transaction becomes two transactions, and the gas fee increases. Finally, atomic transfer can only support assets transformation, but not the information.
3. Cross-chain Bridge Performance Selection
By breaking down the cross-chain bridge mechanism, it can be seen that different cross-chain bridges have distinctive technologies, and there are five aspects to be considered in the performance evaluation:
(1) Security: Taking into account whether there is sufficient decentralization, trust or trustless, the custody style of user funds, and whether there is a risk;
(2) Cross-chain speed: Transaction delay time;
(3) Number of chains: Whether the project itself has a strong team to support the cross-chain function of multiple blockchains, and if it is liquidity pool mode, whether it can provide sufficient liquidity;
(4) Economic efficiency: The cost and difficulty of deployment, and sufficient fees to support the project’s long-term development;
(5) Interoperability: Whether it supports enough Tokens or NFT asset, and whether it can support the cross-chain invocation of smart contracts.
For the above characteristics, we briefly introduce some characteristics of the current mainstream cross-chain bridges and create a scoring table, with each scoring range spanning 0~5 points:
Multi-chain: External validators, based on SMPC and TSS technology, provide peg token or original token through liquidity pool, support 56 chains, TVL: $2.65B, support NFT and tokens more than 2000, and 24 nodes in the system. Fees: 0.01%.
Wormhole: 19 external validators and multi-signature technology to guarantee security, asset transfer model mechanism is lock-mint/burn, supports EVM and non-EVM chains, supports 10 chains and TVL: $444M. Fees: $0.0001.
Connext: Decentralized third party, secured by an off-chain peer-to-peer network of nodes (54 routers), asset transfer model mechanism is atomic transfer, supports 17 chains including EVM chains and Layer2 solutions, TVL: $35M. No fees for users.
Hop: External validators, support for layer 2 solutions and ERC-20 tokens, asset transfer model mechanism is liquidity pool, Fees: More than $1.
deBridge: Decentralized third party, multi-sig technology, pledge mechanism used to further ensure security; asset transfer model mechanism is lock-mint/burn; assets are locked in the smart contract of deBridge, supports 7 chains and 81 tokens.
Cosmos IBC: Light clients and relays, offers original asset in cosmos system and supports all cosmos zones and EVM chains.
Rainbow bridge: Light clients and relays, only support Near and Ethereum, asset transfer model mechanism is lock-mint/burn. Fees: less than $1.
Nomad: Light clients and relays, deploys smart contract to manage messages, many off-chain roles to secure the network, based on Connext’s asset, supports 7 chains, no fees.
LayerZero: Decentralized third party, the basic layer of cross-chain Apps, supports all chains in theoretically with high deployment cost.
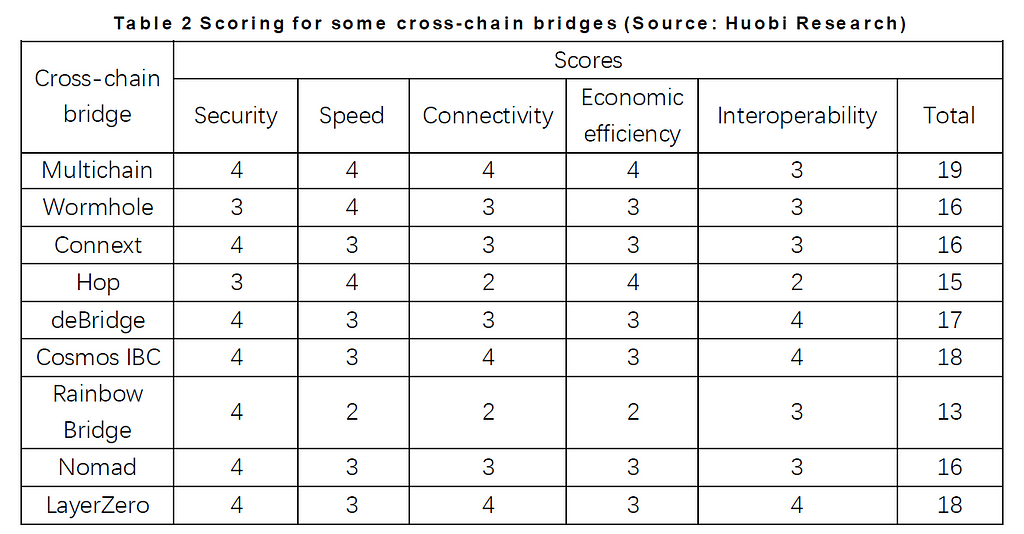
Although cross-chain bridges aim for high scores in the above performance evaluations, like the performance of blockchains, it also faces the trilemma of universality, scalability, and trustlessness. This was proposed by Arjun Bhuptani. No matter what form the cross-chain bridge takes, it is limited by the trilemma. For example, the cross-chain bridge that pursues the speed of asset transfer may sacrifice security.
In fact, the most important criteria for users when choosing a cross-chain bridge are cost, followed by speed and security. Security decreases from light client/relay, multi-point verification to single-point verification. With the exception of the above, security also depends on whether there are bugs in the cross-chain smart contract, but this cannot be discovered by ordinary users. In addition, under the validator mechanism, whether the validator needs to pledge to participate in the transaction verification process is also a user consideration. A cross-chain bridge with a pledge mechanism is safer because the pledged assets would be confiscated once a validator does something bad. This brings a certain sense of security to users, and also increases the cost of misconduct for validators. Some cross-chain bridges also have an “insurance mechanism”, and the slashed assets of the validator will be used to compensate for the losses of users.
3.1 Time duration for cross-chain
For cross-chain transactions to be effectively confirmed on the blockchain, the cross-chain bridge usually sets the delay time. Alternatively, some cross-chain bridges will set up a window period, such as Arbitrum bridge. To save the gas fee, some protocols will wait for a long time to collectively package the cross-chain information. For example, the relay of the Rainbow bridge only updates the cross-chain information every 16 hours.
However, some protocols sacrifice security for the speed of transactions, and both Connext and Hop reduce waiting time by allowing other market participants to send tokens directly to the recipient before the fraud proof window expires. In fact, these two protocols bear the risk of malicious transactions, so that they can charge users for speed.
3.2 Fees
At present, most cross-chain fees still come from the gas fee on-chain. Because most off-chain roles are the cross-chain projects themselves, little or no cross-chain fees are charged. For example, Wormhole charges $0.0001, and Nomad does not charge any cross-chain fees. But this is not a long-term solution, because if the relayer is always undertaken by the official, it will undermine the very concept of decentralization. Like Nomad, it has four off-chain roles, and needs other chains to record cross-chain information. Although this ensures security and decentralization to a certain extent, the cost is extremely high. If the project does not charge fees, it will be unsustainable. Low fees are a way for cross-chain bridges to attract users, but it also shows that the cross-chain bridge market is highly competitive. If the cross-chain project itself needs to issue tokens, the fee is a good way to capture economic value, and it also needs the cooperation of the tokenomics.
3.3 Security and risks
The risks of the cross-chain bridge mainly come from four aspects: 1. Hacker attacks; 2. Liquidity pool problem; 3. Risks on blockchains deployed by the cross-chain bridge (such as Terra crash); 4. Downtime or delay (minimize the use of “trust-based” or “optimistic” cross-chain bridges). The main targets of cross-chain bridges being hacked are: 1. Smart contract bugs; 2. Cross-chain verification methods or intermediate process. This year, the Ronin cross-chain bridge was attacked because five of the nine validators’ private keys were stolen. The official team ran four of the validators. The table below summarizes some of the major cross-chain bridge hacking incidents.
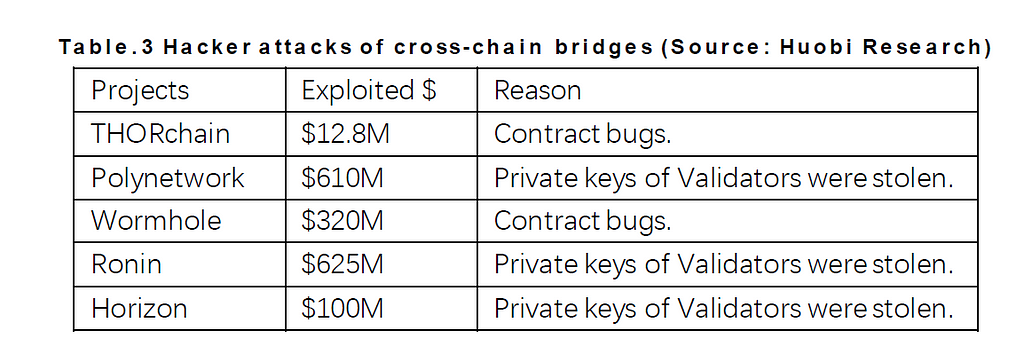
Security must be a primary direction for the continuous evolution of cross-chain bridges. This is because once an attack occurs, it results in not only the loss of the cross-chain project itself, but also significantly affects the assets on-chain. For example, the “wrapped” tokens may become worthless, and protocols on-chain cannot respond quickly, resulting in a huge arbitrage opportunity. From the perspective of the cross-chain bridge verification mechanism, MPC technology is safer than multi-sig. Even if a validator’s private key is stolen, the attacker cannot decipher the complete private key.
4. The Future of Interoperability: Cross-chain Smart Contracts
From the breaking down of the cross-chain bridge mechanism to the discussion on how to choose a cross-chain bridge, we can see some problems: 1. The contradiction between decentralization and challenges in deployment; 2. The asset guarantee of the cross-chain liquidity pool; 3. How cross-chain fees sustain the development of the project itself; 4. Interoperability is still at a nascent stage; 5. Security issues. With more new public chains, there may be a new mechanism for cross-chain bridges in the future that offers security, flexibility and efficiency. Applications in new forms will also appear. The current bear market may also eliminate a number of cross-chain bridges with poor security, low efficiency and high cost. At the same time, the coming ETH2.0 may also lead to a new Layer 2 cross-chain bridge. We can look forward to many developments.
Due to the multi-chain situation, many smart contracts adopt a strategy of multi-chain deployment. For the protocol, it can attract different user groups and experiment with new features on low-cost chains. For the chain, a powerful application can attract users and meet the needs of other protocols. These multi-chains are generally EVM-compatible, and the protocols deployed on multi-chains are mostly well-known DeFi protocols on Ethereum, such as Curve, AAVE, etc. However, these protocols are independent from each other, apart from the fact that they all belong to the same team. This phenomenon of ledger isolation also brings certain problems. Taking AMM DEX as an example, the newly deployed protocol copy will definitely have insufficient liquidity, resulting in excessive slippage.
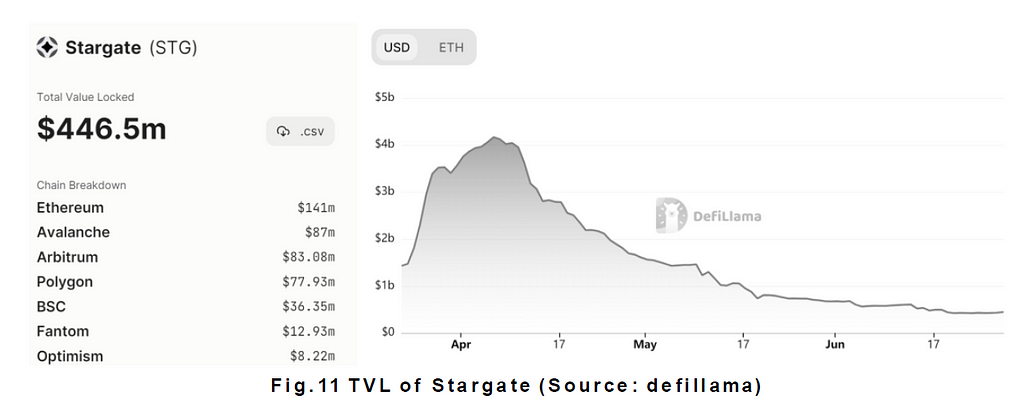
The ultimate goal of cross-chain interoperability is to realize the mutual invocation of smart contracts on different blockchains. This is also the end of the solution to the fragmentation of multi-chain deployed protocols. Now a new concept has emerged: cross-chain smart contracts. This updates the design architecture of Dapps. Cross-chain smart contracts are composed of smart contracts deployed on different chains, they can communicate with each other, and together they form an application as a whole, rather than a copy of an App. The advantages of cross-chain smart contracts are: 1. The ledgers are shared with each other to improve user experience; 2. Developers can take advantage of different blockchains to assign different tasks; 3. More scenarios and development potential for cross-chain Dapps. Chainlink has done some preliminary discussions on cross-chain smart contracts, and is developing a global open-source standard for cross-chain communication. This is similar to Stargate. This full-chain DEX supports cross-chain transactions of stablecoins. It is built on LayerZero, and liquidity pools on different chains can share ledgers. However, Stargate did attract a lot of funds at launch, but its follow-up development was weak. From this point of view, cross-chain smart contracts not only require more stable cross-chain solutions, but more importantly, need application scenarios that truly meet user needs.
Reference
1. https://www.infoq.cn/article/qq5dq6ft2czccje3wb79p
2. https://www.coinvoice.cn/articles/22679
3. https://zhuanlan.zhihu.com/p/110474591
4. https://www.51cto.com/article/702911.html
5. https://docs.multichain.org/getting-started/how-it-works/cross-chain-bridge
6.https://www.xhuqk.com/fileXHDXXBZKB/journal/article/xhdxxbzrkxb/2021/3/PDF/3845.pdf
7. https://blog.chain.link/cross-chain-smart-contracts/
8. https://medium.com/1kxnetwork/blockchain-bridges-5db6afac44f8
9.https://token.im/blog/zh-cn/articles/7742536672153
About Huobi Research Institute
Huobi Blockchain Application Research Institute (referred to as “Huobi Research Institute”) was established in April 2016. Since March 2018, it has been committed to comprehensively expanding the research and exploration of various fields of blockchain. As the research object, the research goal is to accelerate the research and development of blockchain technology, promote the application of blockchain industry, and promote the ecological optimization of the blockchain industry. The main research content includes industry trends, technology paths, application innovations in the blockchain field, Model exploration, etc. Based on the principles of public welfare, rigor and innovation, Huobi Research Institute will carry out extensive and in-depth cooperation with governments, enterprises, universities and other institutions through various forms to build a research platform covering the complete industrial chain of the blockchain. Industry professionals provide a solid theoretical basis and trend judgments to promote the healthy and sustainable development of the entire blockchain industry.
Official website:
Consulting email:
research@huobi.com
Twitter: @Huobi_Research
https://twitter.com/Huobi_Research
Medium: Huobi Research
https://medium.com/huobi-research
Disclaimer
1. The author of this report and his organization do not have any relationship that affects the objectivity, independence, and fairness of the report with other third parties involved in this report.
2. The information and data cited in this report are from compliance channels. The sources of the information and data are considered reliable by the author, and necessary verifications have been made for their authenticity, accuracy and completeness, but the author makes no guarantee for their authenticity, accuracy or completeness.
3. The content of the report is for reference only, and the facts and opinions in the report do not constitute business, investment and other related recommendations. The author does not assume any responsibility for the losses caused by the use of the contents of this report, unless clearly stipulated by laws and regulations. Readers should not only make business and investment decisions based on this report, nor should they lose their ability to make independent judgments based on this report.
4. The information, opinions and inferences contained in this report only reflect the judgments of the researchers on the date of finalizing this report. In the future, based on industry changes and data and information updates, there is the possibility of updates of opinions and judgments.
5. The copyright of this report is only owned by Huobi Blockchain Research Institute. If you need to quote the content of this report, please indicate the source. If you need a large amount of reference, please inform in advance (see “About Huobi Blockchain Research Institute” for contact information) and use it within the allowed scope. Under no circumstances shall this report be quoted, deleted or modified contrary to the original intent.
The Foundation of Inter-chain Value Flow: Interpretation of Cross-chain Solutions was originally published in Huobi Research on Medium, where people are continuing the conversation by highlighting and responding to this story.
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.