Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.
Inside Privacy Pools: Vitalik Butterin’s New Proposal to Balance Blockchain Privacy and Regulatory Compliance
The protocol combines some of the ideas of Tornado Cash with ZK-SNARKS to provide a native, non-invasive approach to enable regulatory checkpoints in blockchainprotocols.

Created Using Midjourney
The friction between the anonymity of blockchain protocols, especially DeFi, and regulatory requirements has been one of those endless debates in the digital assets space. There is very little doubt that some level of regulatory checkpoints in the form of KYC/AML is needed to unlock the mainstream adoption of crypto. At the same token, privacy and anonymity are some of the most desired properties that are at the core of the crypto ethos.
One of the most creative angles of the privacy-vs-regulation debate is to explore some novel ways to enable regulatory checkpoints without the need of brute force KYC/AML. A few months ago, I wrote an article about these ideas in CoinDesk. Recently, Ethereum creator Vitalik Butterin collaborated with early Tornado Cash contributor Ameen Soleimani, Chainalysis’ Jacob Illum and two researchers from the University of Basel on a paper that outlines a new interesting idea that balances privacy and regulatory compliance in blockchain protocols. Under the catchy name of privacy pool, the approach borrows a few ideas from Tornado Cash and combines them with ZK-SNARK into a very intuitive protocol.
Let’s explore.
Inside Privacy Pools
At its essence, Privacy Pools operate based on the principle of enabling a user to demonstrate membership in a predetermined association set rather than simply presenting zero-knowledge evidence of a link between a withdrawal and a prior deposit.
The conceptual framework of these pools encompasses various forms of association sets: from the entirety of previous deposits to an isolated, user-specific deposit, or any intermediary range. Crucially, the chosen set is indicated through the public input of a Merkle root.
In the interest of clarity, it’s important to note that a direct proof verifying that the association set is a genuine subset of preceding deposits isn’t provided. Instead, two zero-knowledge proofs of Merkle branches are necessitated, both of which employ the identical coin ID as a leaf:
I. A Merkle branch tied to R, signifying the complete set of coin IDs.
II. A Merkle branch connected to the provided association set root, RA.
The underlying intention mandates the entire association set to be accessible, potentially on-chain or through an alternative medium. This foundational principle enables users to offer a potential source range for their funds without stipulating a precise deposit or, at the opposite end, without presenting any information except a non-double-spending proof.
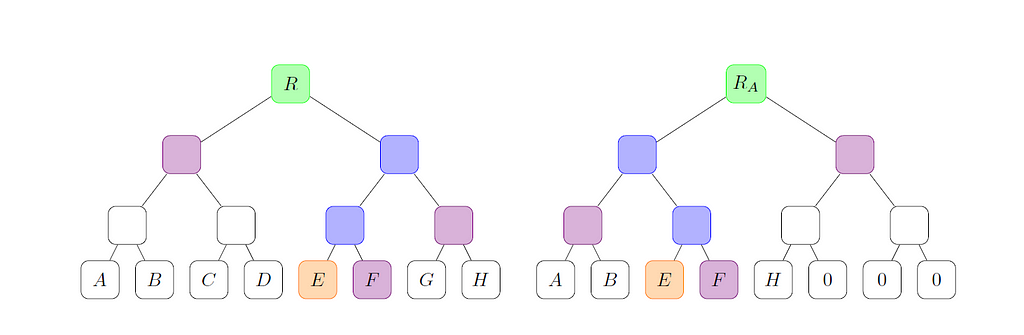
Image Source: https://papers.ssrn.com/sol3/papers.cfm?abstract_id=4563364
Methods of Association Set Formulation
Conceptually, there exist two primary techniques to generate these sets:
I. Inclusion (or membership): This involves identifying a distinct collection of deposits perceived as low-risk based on concrete evidence and subsequently crafting an association set limited to these deposits.
II. Exclusion: Here, specific deposits deemed high-risk based on tangible evidence are identified. The resultant association set encompasses all deposits excluding the high-risk ones.
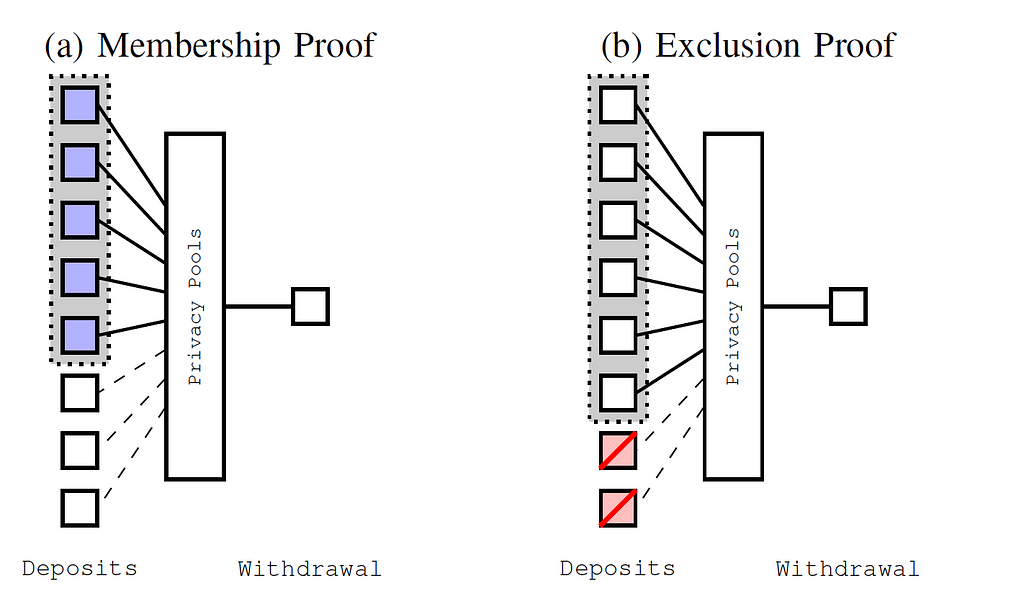
Image Source: https://papers.ssrn.com/sol3/papers.cfm?abstract_id=4563364
A Practical Illustration
To further elucidate, consider a scenario involving five participants: Alice, Bob, Carl, David, and Eve. The quartet, comprising Alice, Bob, Carl, and David, are recognized as genuine users, valuing privacy, while Eve is known for her illicit activities. Though her real identity remains a mystery, there’s substantial evidence linking “Eve” to stolen assets, a situation reminiscent of illicit funds identified in Tornado Cash, which frequently originate from public blockchain-visible DeFi protocol exploits.
Upon withdrawing, every user possesses the autonomy to designate their association set. It’s mandatory to encompass their individual deposit, but the inclusion of other addresses remains discretionary. Considering the motivations of Alice, Bob, Carl, and David, the dual objectives are clear: maximizing privacy while ensuring their assets aren’t deemed dubious. Their optimal strategy becomes apparent: exclude Eve from their association set, resulting in an association set comprising {Alice, Bob, Carl, David}.
Eve, motivated by a similar desire to augment her association set, finds herself in a quandary. Excluding her deposit isn’t an option, thereby compelling her to adopt an association set that includes all five deposits.
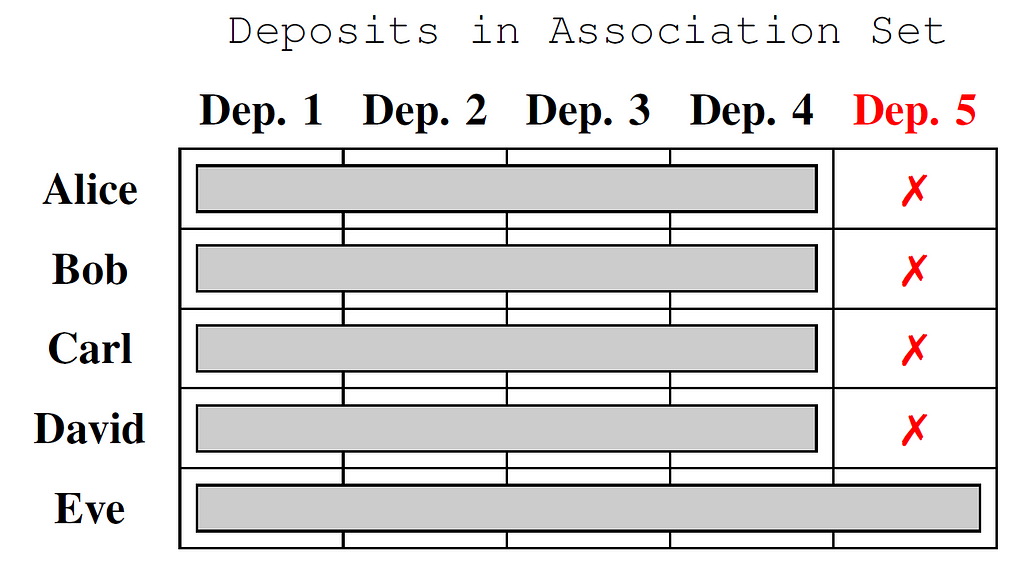
Image Source: https://papers.ssrn.com/sol3/papers.cfm?abstract_id=4563364
Privacy Pools is one of the most interesting approaches to balance privacy and regulatory compliance in blockchain protocols. The idea of association sets is non-invasive and can be easily added into most blockchain protocols such as DeFi. Compared to brute force KYC/AML, privacy pools are a native on-chain mechanism that can start bridging the gap between regulation and the crypto world.
Inside Privacy Pools: Vitalik Butterin’s New Proposal to Balance Blockchain Privacy and Regulatory… was originally published in IntoTheBlock on Medium, where people are continuing the conversation by highlighting and responding to this story.
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.