Latest news about Bitcoin and all cryptocurrencies. Your daily crypto news habit.
 Photo by Peter Gonzalez on Unsplash
Photo by Peter Gonzalez on UnsplashDistributed Ledgers
The adoption of blockchain as a technology is gaining traction. One of the advantages of the system is the unique distributed ledgers that are secured through cryptographical solutions. These are almost unhackable using even the most advanced supercomputers available to us today.
Yet this doesn’t mean it will never be unbreakable, that somehow, by dark means, hackers will infiltrate the blockchain.
With the advent of, and development in, quantum architectural systems (QAS), blockchain could possibly meet its nemesis.
Maybe not today, or tomorrow, but someday soon.
And the threat needs to be addressed.
These are strong words, but valid ones if we take Hartmut Neven, a physicist at Google, and his opinion on the subject seriously.
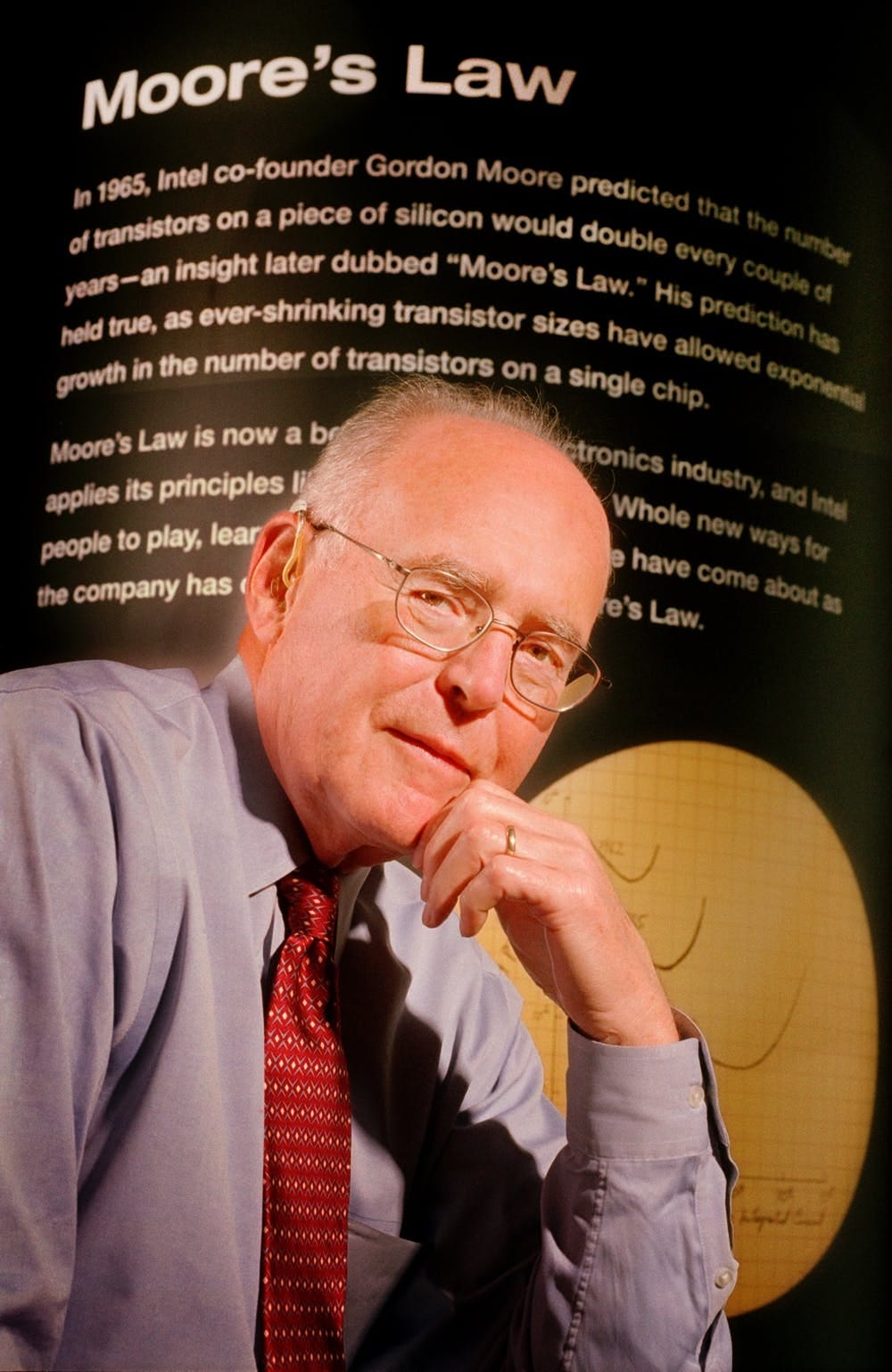
Moore’s Law’s Death
According to the German, the belief that Moore’s Law — the law which states the number of transistors in a dense integrated circuit doubles approximately every two years — is still the de facto technological reality is a false one. He has gone on the record by claiming quantum computers are advancing at such a rate their computational power is ‘doubly exponential’, meaning instead of exponential growth by powers of 2, quantities — or computational power with the ever-important qubits grow by ‘powers of powers of 2’, initializing a paradigmatic shift in both attitudes to quantum systems and how we safeguard them from menaces. His discovery has been so influential in quantum computer circles, in fact, that a new law has been named after him, Neven’s Law, which has blown Mr Moore out of the water.
It also means Quantum Supremacy, the belief that quantum architectural devices could solve conundrums classical computers have failed to do thus far, could be a reality.
At the moment, however, contemporary technology adopting blockchain systems has been free from hacking and other incursions, though it would be a mistake for developers in the blockchain sphere to sleep on their laurels and assume the technology at their fingertips is foolproof from the external threat at some time in the future.
‘Online identity and reputation will be decentralized. We will own the data that belongs to us.’ — William Mougayar, author The Business Blockchain: Promise, Practice, and Application of the Next Internet Technology
Neven’s discovery has just confirmed blockchain technology will have to step up its game if it is to become the go-to solution for industries wanting to implement it into their business models in the coming years.
Weaknesses
Being cryptographically secure under current technology is all well and good, but this paradigm shift is a fair warning, especially for developers and businesses in Bitcoin and other cryptocurrencies, where any weakness in the system’s blockchain architecture could equate to hackers having free access to the wealth across the distributed ledger systems.
But what is a quantum computer?
Bits and Qubits
A quantum device is a machine that aligns to the principles of quantum mechanics to carry out calculations. Traditionally, classical computers use the binary system of bits, which can only represent two states, either ‘1’ or ‘0’, ‘on’ or ‘off’. Quantum computers, on the other hand, operate with quantum bits, often called ‘qubits’, which because of their quantum essence — which is altogether strange and fantastic — can be 0, 1 or any state between these two. This is called superposition, and this phenomenon lets quantum computers execute calculations in a fraction of the time even the best supercomputer on the planet can achieve.
A second, equally important, aspect of quantum theory is entanglement. This is when two qubits, irrespective of the distance between them in physical space, become one, or ‘entangled’, influencing each other. The magic of this is the entangled qubits produce exponential power, far more than what bits can muster in the binary system.
There’s the theory.
In practical terms, however, harnessing the power of qubits in their superposition and entangled states by applying methods using microwaves and laser beams are difficult to achieve, but once the state has been established, the real problem begins: in their entangled state qubits are very sensitive to ‘outside noise’, by that changes in temperature and electromagnetic waves, which cause errors. Hence the term ‘decoherence’. This is still an intractable problem when developing quantum architectural systems.
As with classical computers and bits, quantum computer processors are measured in how many qubits can be harnassed at any on time.
Since the first experiments more than twenty years ago, the qubit power of quantum processors has grown exponentially.
So what implications does this have for the blockchain in the future?
Encryption Threat
The confidence and trust some have in the blockchain are worthy of celebration. There has been nothing like it in history. The underlying technology that supported Satoshi Nakamoto’s Bitcoin, so far, has done what it has always set out to do. Startups realize what the technology can do for logistics, data, medicine and countless other industries in the future will be for the good.
With current computing power, the blockchain is a solid solution and it seems unlikely its integrity will be compromised. What is a threat, though, is when, not if, quantum processing power reaches quantum supremacy, which would enable it, for example, to find the prime factors of infinitely high positive integers, then we would definitely see the security that the blockchain presently guarantees, and the encryption used to safeguard the system, exploited in some way.
Blockchain security at its core depends on functions which are one way. They are designed, in essence, to validate transactions as well as digital signatures on the blockchain. Classical computers have no problem calculating these one way, yet have problems factoring calculations in reverse. Quantum computers, on the other hand, would find these calculations child’s play, creating a scenario for any cybercriminal out there who possesses a functioning quantum device to carry out illicit activities such the validation of double-spending, gaining access to people’s personal assets through the forging of their signatures and exploiting the said person’s details online.
What is needed, then, is for blockchain systems to steam ahead, creating encryption systems which could combat the threat of quantum processing power that, while not having the ability to hack into existing blockchain encryption, will have in the future.
Prevention is a cure.
Kiwi Solution
New Zealand-based scientists, Matt Visser and Del Rajan, came up with a revolutionary idea earlier this year. It is to abandon the idea of creating a cryptographic algorithm based on quantum systems, and rather make the blockchain quantum itself. Naysayers of this believe without a quantum Internet, however, the realization of this project is dead in the water.
Russian Approach
Another proposal, far more down to earth and achievable, has been muted by physicists in Russia, who believe a quantum Internet is the only way to stave off cyberattacks by quantum systems in the future. Yet critics of this stance believe although it is a good idea in essence, the technology at hand is simply not up to the job and the realization of this dream is still decades away.
But we can dream.
Conclusion
We are still far away from blockchain becoming a universally accepted modality used far and wide across business and other areas of our lives. Nonetheless, as more and more people accept it for what it is, a solution for today’s problems in regard to decentralization, transparency and validity of business transactions, there will be a need — cost and labour intensity notwithstanding — to find better encryption solutions to keep the blockchain secure, so that capital markets, the IoT, developer tools, storage security, payment transfer services, content management platforms, social media browsers, and gaming and gambling, to name just a few, run smoothly, without the threat of external attacks from malevolent hackers, making our lives hassle-free, and enriching us positively.
Blockchain Contra Quantum Systems: No Match Made in Heaven was originally published in HackerNoon.com on Medium, where people are continuing the conversation by highlighting and responding to this story.
Disclaimer
The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. Every investment and trading move involves risk - this is especially true for cryptocurrencies given their volatility. We strongly advise our readers to conduct their own research when making a decision.